From Attack Graph to Dollar Figure
Model threats visually.
Simulate losses mathematically.
Report risk financially.
Nodes to Knowledge
Threat modelling you can actually use: our attack graphs turn
hand‑wavy “word pictures” into clear, actionable steps for
managing real cyber risk.
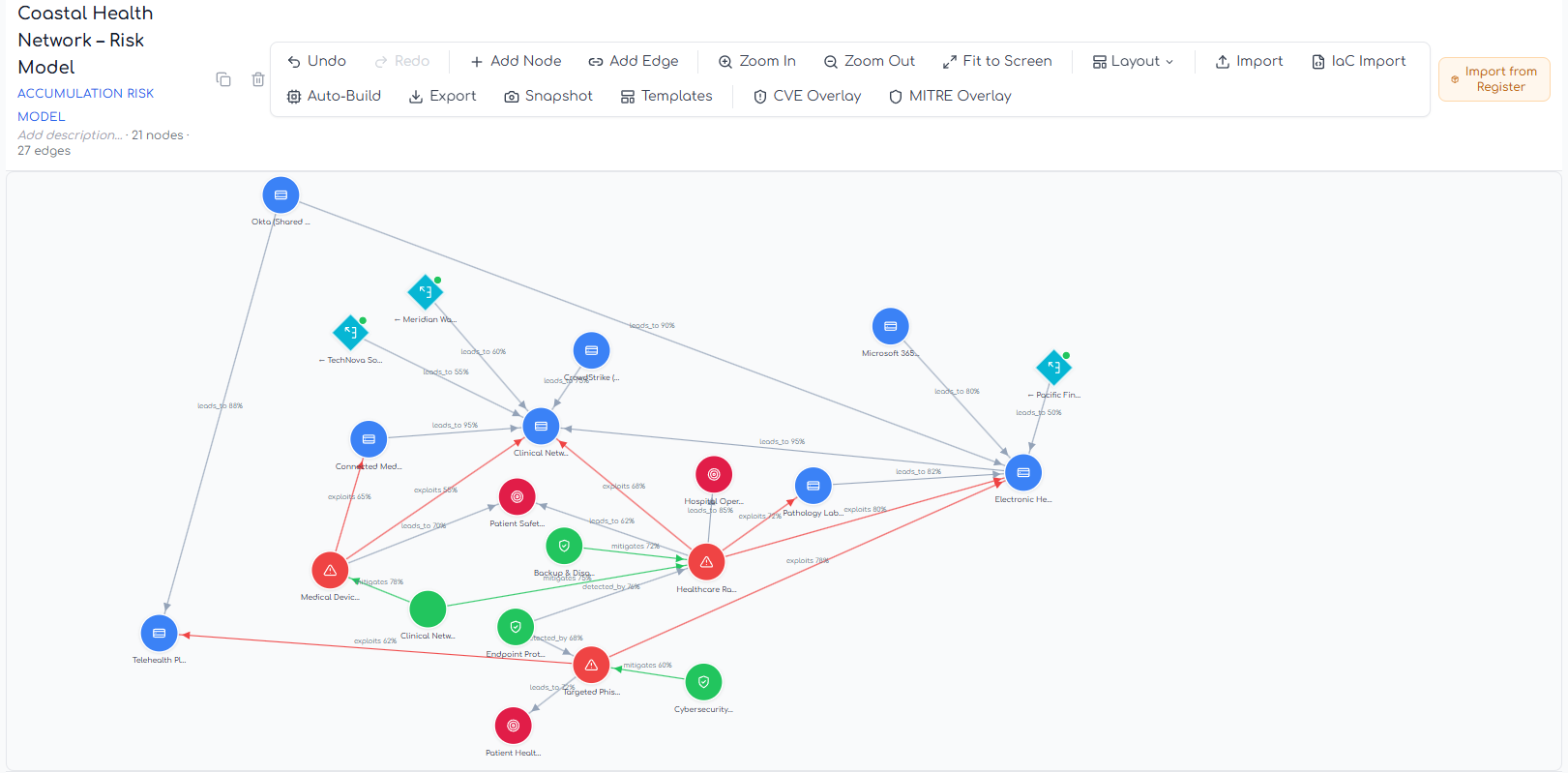
Interactive Canvas
Model risks for new and existing system architectures
Third Party Risk
Cascade risk across graphs to know your true exposure
Probability Propagation
Know your neighbour's risk, know your exposure
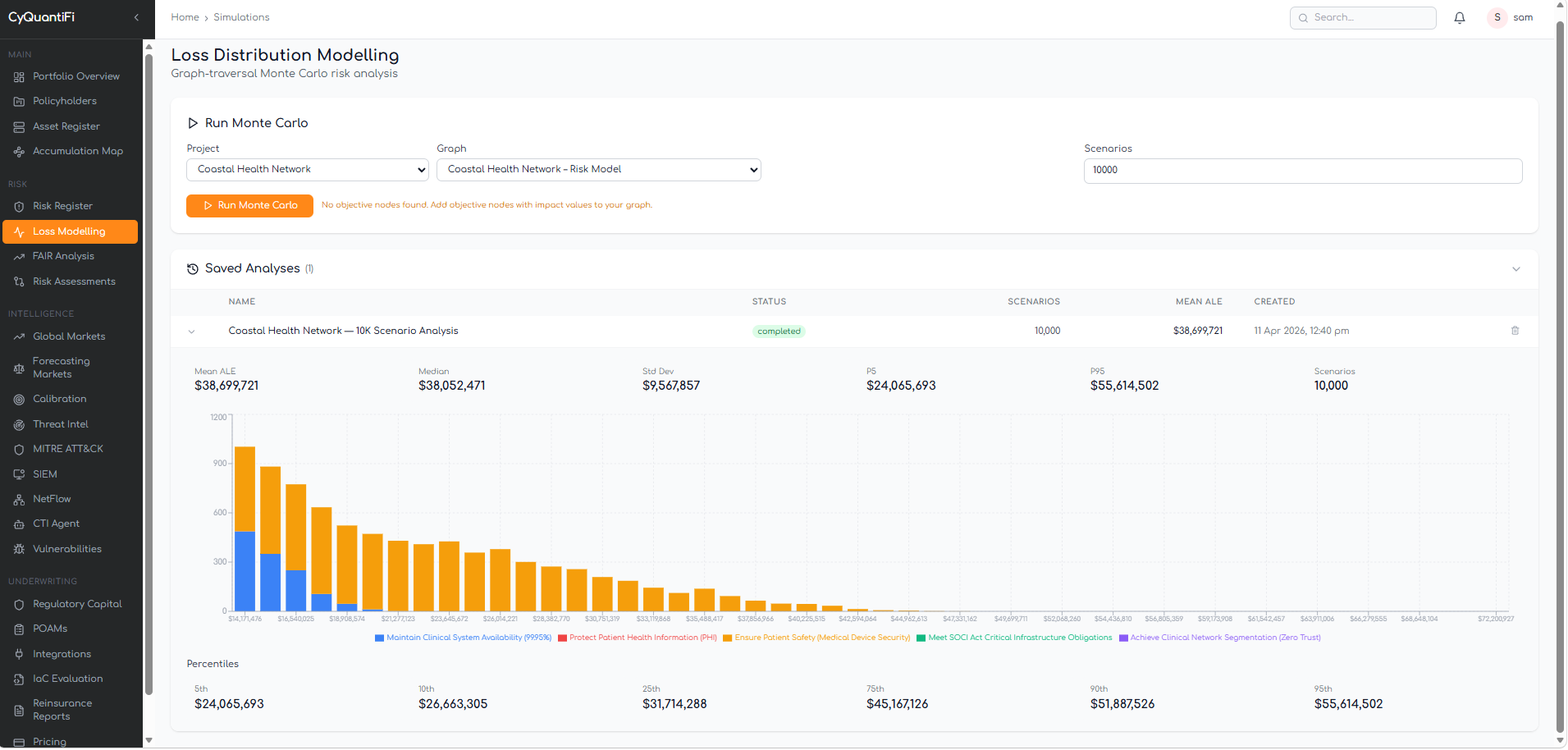
Monte Carlo Simulations
Not just for James Bond.
Run thousands of risk simulations and see exactly how good—or how ugly—it could get.
All translated into dollar values you (and your board) can actually trust.
CISO to Board: Show Me The Money
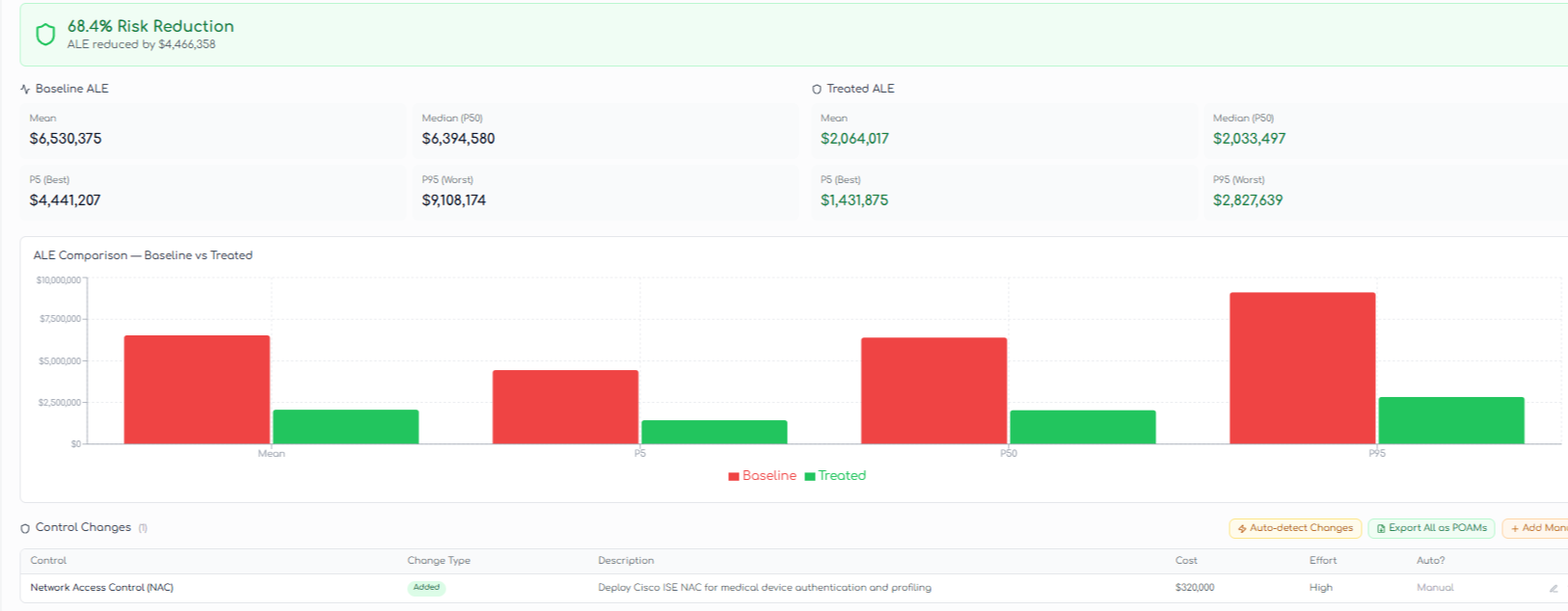
Real ROI
Demonstrate the value of controls by showing how much risk you can prevent.
Real Exposure
Risk reduction and exposure update in real tie as CTI is updated
Seeing is believing: CyQuantiFi-ing is knowing
We’ll model a live scenario from your own environment, because
real risk doesn’t live in a PowerPoint slide
